Windows privilege escalation exploits are used for elevation of privilege locally and runs arbitrary code in kernel mode. In other words, when you have a web backdoor shell on your target server which doesn’t have administrative privileges you would require a exploit to get admin account.
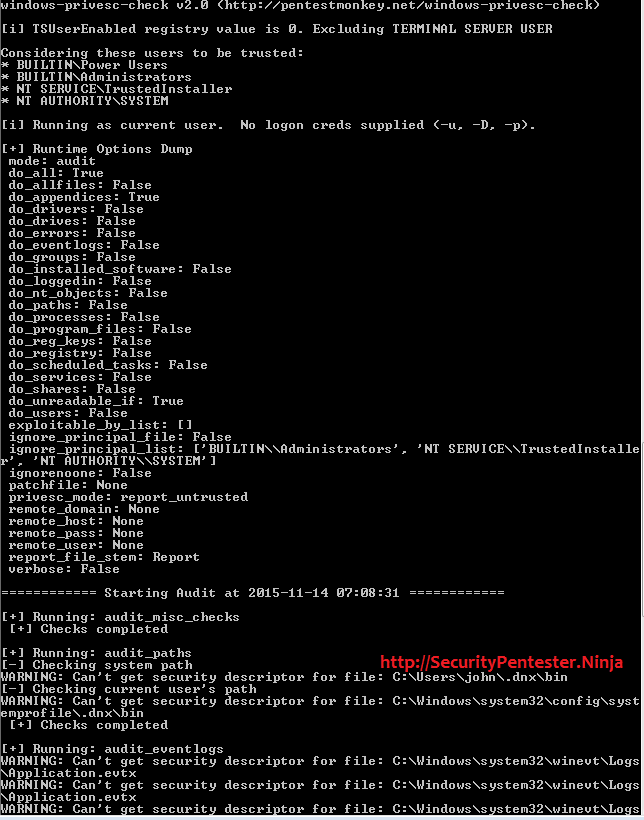
During my many penetration testing experience, at times i am able to upload web backdoor shell, however my goal is to get Administrator level privileges . When ever i upload a web shell, the second file i upload is a Standalone Executable to Check for Simple Privilege Escalation Vectors on Windows Systems. This can be downloaded from https://github.com/pentestmonkey/windows-privesc-check .