Yes, I got my Offensive Security’s OSCP done in the 2nd Week of April. I wasn’t able to blog after that as i was busy with projects. I have read too many blogs after everyone gets done with their OSCP, For me things were very different.
I bought my OSCP with 30 Days lab access for myself, i would recommend that anyone who is planning attempt OSCP and has a experience of at least 2 years manual penetration testing should purchase not more then 30 days access. I think its enough to get going, keeping in mind if you can spend 4-7 hours daily.
It is very important to RTFM rather then watching videos provided by Offensive Security. I started off reading the manual and doing all the exercises till i reached exercise 3 and i shifted to Labs.
In the Lab few machines were tough, when i realized the solution which would work, i was out of time. I found some 59 boxes in total where i was able to get 50 of them. I left 9 boxes in which i had limited access on 2 boxes. The Labs are very challenging, the OffSec guys say Try Harder where as i would say;
Make sure you have enumerated all the services and start from the basic don’t get into complication by trying harder.
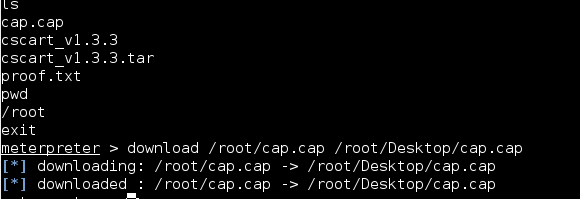
This is my advice to all the students giving OSCP, find the lowest hanging fruit and get it first. I have read in the manuals that the trophies found in machines named proof.txt can only be accessed if you have root / administrator privileges (I dont think so). I found few trophies without getting local privileges on the system. Document everything in keepnote so that when you write your Penetration testing report for the whole network things are easy. Start writing report 3-4 days before your lab expires as if you feel you missed something in keepnote you can work on that specific box again.
proof.txt and cap.cap two trophies in one box
The 3 tough machines (The Big Three) as told by everyone is Pain, Sufferance and Humble, For me Humble took 15hrs , I was done with Pain and Sufferance in 30 min. For the motivation, when i started my LABS i compromised 8 machines on the first day, I didn’t jumped the list still i reached 220. After i was done with Report i spend another 2 days which were left to do some more exercises.
In my report, i made a excel sheet which had all the live IP with the trophies adding colors, making it easy for the Offsec Challenge team find out which ones i got.
THE EXAM
My exam started at 2PM, I thought its the most appropriate time as i was unable to schedule it in the morning. From 2pm till 4pm my anxiety kicked in after reading the exam. I just sat there in front of my laptop reading the pdf which was send by offsec. I didnt do anything at all just ran a nmap scan on the machine and sat there doing nothing, by 4pm i realized i havent done anything at all and i was just sitting looking at the results. Punched myself and started exploiting, started looking for exploits on all of the machines at ones. by 9:30pm i got 2 machines, fast forward …… by 9am i got 4 machines. i was unable to get the 5th one. The exam is very challenging and has real world examples. Best of luck to everyone who is giving the exam.

